Top 8 Secure Messaging Policy Best Practices for Enhanced Security in Healthcare
Efficient communication among healthcare staff is crucial for optimal patient care. As such, mobile devices have become the go-to among care teams for facilitating real-time collaboration. However, traditional text messaging applications pose significant security risks for sensitive patient information.
This is where secure messaging solutions come in. They offer a reliable and HIPAA-compliant platform for healthcare providers to communicate securely, ensuring the protection of patient data remains a top priority. But simply implementing a secure messaging solution isn’t enough. A comprehensive secure messaging policy is essential to optimize security and ensure staff use the platform effectively.

Secure Messaging Policy Best Practices
A well-defined secure messaging policy acts as a roadmap for staff, outlining proper usage protocols and data security best practices. Implementing a secure messaging policy allows employees to use their mobile devices while maintaining security through guidelines that monitor staff usage, security standards and best practices for integration with employee workflows.
Here are the top eight best practices to consider when crafting your secure messaging policy:
1. Mandatory use for protected health information:
Clearly define which types of information are required to be shared through secure messaging. This should include all protected health information (PHI), such as patient names, medical record numbers, social security numbers, and any other data care teams use to identify a patient. Mandating secure messaging for sensitive data minimizes the risk of accidental breaches.
2. Data ownership and access:
Establish clear ownership of data transmitted by staff members through the secure messaging platform. The secure messaging policy should also outline procedures for authorized access to messages for auditing or legal purposes.
3. Secure file sharing:
Text messages aren’t always the most efficient way to share information. The secure messaging policy should address the sharing of images, videos, and documents, ensuring they are transmitted through a secure messaging platform and encrypted just like text-based messages. Additionally, your secure messaging platform should not save images or videos taken on the device to the device’s photo library.
4. Keep data safe:
To protect patient confidentiality, taking screenshots or sharing patient information with users who are not bound by a company’s privacy policy should be strictly prohibited.
5. Consider limitations:
As secure messaging platforms require an internet connection, it’s important to consider the limitations of these platforms when internet access is unavailable or unreliable.
6. Device security measures:
Strong security measures should be in place for mobile devices used for secure messaging, including where and when they can be used, such as restricting the use of shared devices beyond certain boundaries.
7. Secure messaging for personal use:
Remind staff that company policies regarding personal use of work email extend to secure messaging platforms on personal devices. This may include restricting the use of these platforms to work-specific conversations, as well as ensuring secure messaging apps are removed when selling or disposing of a personal device.
8. Data protection:
To protect sensitive information, users must notify their supervisor immediately if a mobile device is lost or stolen. Remote access controls and the ability to sync with your Active Directory ensure that lost or stolen devicescan have their access revoked, ensuring patient data doesn’t fall into the wrong hands.
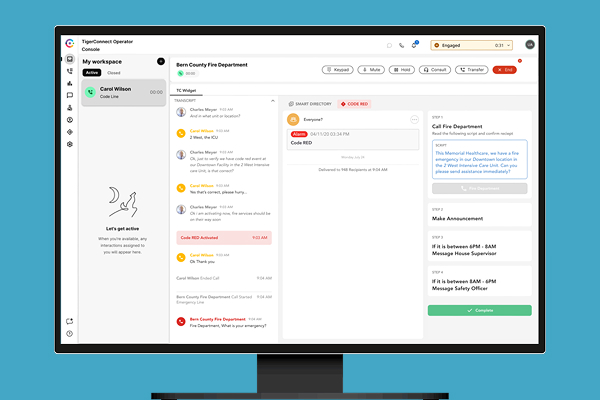
The Evolution of Clinical Communication
By implementing these best practices and utilizing a secure messaging solution like the TigerConnect Clinical Collaboration Platform, which offers end-to-end encryption, role-based access controls, and detailed audit trails, healthcare organizations can improve care team collaboration while protecting patient data and maintaining HIPAA compliance.
However, clinical communication has evolved beyond basic secure messaging over the last several years. Clinical communication and collaboration (CC&C) platforms now offer diverse capabilities such as patient engagement, on-call scheduling, and alarm management, integrate with various clinical systems to break down data silos, and facilitate specific workflows that drastically improve patient outcomes and care team efficiency. As such, it’s important to understand what to look for in a CC&C solution so that your organization can make the right investment. Choosing a CC&C platform can feel like a difficult task, but our helpful guides will ensure you’re applying the right framework when evaluating your options.
Learn more about Clinical Collaboration Software Platform, Resident Scheduling Software, Physician Scheduling Software, Alarm Management & Event Notification Software & Patient Engagement Software.
Featured Resources
Related Articles

What to look for in a CC&C solution
Discover the eight areas you must consider to provide value to your organization with a CC&C solution.