What Is HIPAA Compliance and Where Is It Taking Health IT?
Digital technology makes healthcare organizations more effective and efficient, reducing the potential for human error and speeding clinical communications. But it can also threaten patient privacy. Congress recognized this risk in the mid-90s — a decade before smartphones and nearly 15 years before required electronic health records (EHR) — and passed the Health Insurance Portability and Accountability Act of 1996 (HIPAA). This legislation sets national standards for patient privacy and, eventually, for healthcare data security as well.
Since then, digital technology has rapidly evolved, and so has HIPAA IT compliance.
What is HIPAA compliance? What are the rules and the consequences of breaking those rules? And what are the HIPAA compliance requirements that IT leaders need to understand?
What Is HIPAA Compliance?
In the beginning, healthcare providers were the only ones who needed to be well-versed on HIPAA requirements. Now, understanding HIPAA compliance is a priority for healthcare IT departments as well.
HIPAA legislation was initially created to “improve the portability and accountability of health insurance coverage” when people changed jobs. It also included Administrative Simplification provisions to reduce healthcare fraud and waste. Since then, the federal government has added a series of rules related to patient privacy and data security. These rules help to ensure that healthcare organizations effectively secure their patients’ protected health information (PHI) — names, phone numbers, birthdates, Social Security Numbers, and any other data that can be used to identify an individual patient.
The U.S. Department of Health and Human Services (HHS) regulates HIPAA compliance, and the HHS Office of Civil Rights (OCR) enforces the HIPAA Rules. OCR provides compliance guidance, investigates possible HIPAA violations, and takes action against non-compliant organizations.
Sometimes that action comes in the form of a written warning or technical assistance, but there’s often a hefty fine. Depending on the severity of the violation, organizations can be fined between $25,000 and $250,000. OCR penalized 10 organizations in 2019, with fines totaling $12.27 million.
Who Is Subject to HIPAA Regulation?
HIPAA regulations apply to individuals or organizations that meet the definition of a “Covered Entity” or a “Business Associate.”
Covered Entities are healthcare entities that create, maintain, or transmit PHI, including:
- Healthcare providers — doctors, dentists, clinics, psychologists, nursing homes, chiropractors, and pharmacies that transmit electronic PHI
- Health plans — health insurance companies, HMOs, corporate health plans, and government health plans (e.g., Medicare, Medicaid, TriCare)
- Healthcare clearinghouses — entities that process nonstandard health information received from another entity into a standard format, or vice versa
Business Associates are individuals or institutions that perform certain business functions or activities on behalf of covered entities, requiring them to have access to PHI. Business associates might include:
- Third-party administrators or claims processors
- EHR and clinical communications software providers
- Data aggregators or data analysis providers
- Cloud storage providers
- Email encryption services
- Billing or CPA firms
- Attorneys
- Independent medical transcriptionists, IT contractors, and other non-employee consultants with access to PHI
Before business associates can legally handle PHI, they must have a written business associate contract (BAC) with the covered entity. The BAC establishes exactly what the business associate will do with the data and requires strict HIPAA compliance.
What Are the HIPAA Rules?
What is HIPAA compliance? The answer to that question has changed dramatically in the quarter-century since it was first enacted. Since then, HHS has instituted a series of HIPAA Rules that have little (if anything) to do with health insurance portability. These rules include:
- HIPAA Privacy Rule: The Privacy Rule sets national standards for when PHI may be used and disclosed and grants patients the right to access their data. It also requires providers to develop and implement written privacy policies, to notify patients (in writing) about these policies, and to provide annual HIPAA training for staff.
- HIPAA Security Rule: The Security Rule outlines administrative, physical, and technical safeguards that covered entities and Business Associates must have in place to secure electronic protected health information (ePHI).
- HIPAA Enforcement Rule: The Enforcement Rule empowers OCR to enforce the privacy and security rules by investigating HIPAA complaints, conducting compliance reviews, performing education and outreach, and levying financial penalties. OCR also works with the Department of Justice to refer possible criminal violations of HIPAA.
- HIPAA Omnibus Rule: The Omnibus Rule of 2013 clarifies the role of business associates, which were not previously subject to HIPAA rules, and outlines the criteria for Business Associate Agreements. It includes provisions required by the Health Information Technology for Economic and Clinical Health (HITECH) Act to strengthen HIPAA security and privacy protections.
- HIPAA Breach Notification Rule: The Breach Notification Rule requires covered entities and business associates to notify OCR when PHI is breached. This rule also distinguishes between “minor breaches” (those affecting fewer than 500 people) and “meaningful breaches” (those affecting more than 500 individuals). HIPAA requires organizations to report both types of breaches to OCR, but the protocol is different, and all meaningful breaches are made public on OCR’s Breach Notification Portal, or “Wall of Shame.”
How to Comply with HIPAA
What is HIPAA compliance? It’s more than merely following the rules. HIPAA-beholden entities must also prove they’re following the rules and doing their best to prevent possible data breaches.
To help Covered Entities and Business Associates meet HIPAA IT compliance requirements, HHS has outlined “The Seven Fundamental Elements of an Effective Compliance Program.” These elements include:
1. Implement written policies, procedures, and standards of conduct.
Organizations must develop internal HIPAA policies and procedures to ensure compliance with all HIPAA Rules. These policies must be documented and regularly updated. Organizations must document all HIPAA compliance efforts, including HIPAA office guidelines, self-audits, remediation plans, and staff training sessions. OCR will want to see this information during HIPAA investigations or audits.
2. Designate a compliance officer and compliance committee.
HIPAA compliance is complicated, and the stakes are high. It helps to have one person overseeing the process, with the support of an interdisciplinary compliance committee that can provide the information and resources needed to meet HIPAA requirements.
3. Conduct effective training and education.
Both covered entities and business associates are required to conduct annual staff training on HIPAA office guidelines. Employees must attest (in writing) that they understand HIPAA policies and procedures.
4. Develop effective lines of communication.
HIPAA compliance is a group effort and must be a priority for everyone in healthcare — from administrative leadership, to medical professionals, to IT departments. Annual training is not enough to ensure it’s top of mind for staff. It must be part of the culture, supported by technology. (For example, instead of just telling employees not to send text messages with PHI, hospitals can provide HIPAA compliant texting solutions.)
5. Conduct internal monitoring and auditing.
Organizations must conduct annual self-audits to assess how well they’re meeting HIPAA standards and identify gaps in their Administrative, Technical, and Physical safeguards. Then they must create written remediation plans to address those gaps and correct any HIPAA violations.
6. Enforce standards through well-publicized disciplinary guidelines.
HIPAA requirements are complex and ever-changing, and organizations often learn as they go. By sharing new insights and standards with frontline employees, leaders can help ensure everyone in the organization understands the importance of HIPAA compliance and their role in achieving it.
7. Respond promptly to detected offenses and take corrective action.
Organizations must have a documented breach notification process that explains how data breaches will be reported to OCR and how patients will be notified about compromised data.
Common HIPAA Violations
A HIPAA violation is any data breach that compromises the privacy of PHI or ePHI, but all HIPAA violations are not created equal. They can be minor breaches (a nurse gossiping about a patient and compromising one person’s privacy), major breaches (a hacker accessing thousands of patients’ PHI), and accidental breaches (a doctor discussing PHI with a colleague in an elevator where others can hear).
The most common HIPAA violations fall into the following categories:
Impermissible PHI Use and Disclosure
HIPAA Privacy Rule “Use and Disclosure” violations are among the most common breaches. This happens anytime a healthcare provider or Business Associate shares PHI with someone who is not permitted to have that information. Sentara Hospitals, for example, was fined $2.175 million last year when the health system sent bills containing PHI to the wrong patients and then failed to accurately report the number of affected individuals.
Use or Disclosure of More than the “Minimum Necessary” PHI
Just because someone works for a covered entity or business associate doesn’t mean they’re allowed to view all patient data. The HIPAA Privacy Rule includes a “minimum necessary” provision, which basically states PHI should be viewed and shared on a need-to-know basis. For example, an IT technician performing routine updates on the EHR system doesn’t need to access patient records to do the job. A billing clerk needs to know which services were performed but doesn’t need to view the results of patient lab work, while clinicians don’t need to view backend systems with patient billing information or Social Security numbers. That’s why it’s important for HIPAA-beholden entities to leverage strict access controls that limit PHI access based on roles, responsibilities, and relevant care team members.
Lack of PHI Safeguards
Medical data is valuable on the black market, making healthcare providers an increasingly popular target for hacking and phishing. In Q4 of last year, ransomware attacks against healthcare providers grew by 350 percent, according to a recent Corvus report. Lost or stolen devices containing PHI and unsecured wireless networks can also compromise PHI. The HIPAA Security Rule lays out administrative, physical, and technical safeguards that organizations must have in place to help protect their data from these attacks. If data is breached and safeguards weren’t in place, organizations can receive hefty fines.
Lack of Individuals’ Access to Their PHI
The HIPAA Privacy Rule grants individuals the right to review and obtain copies of their PHI and most of their medical records. When healthcare organizations fail to provide that information in a timely manner or charge patients unreasonable fees for copies of their records, they commit one of the most common HIPAA violations. Fifty-one percent of healthcare organizations are not fully compliant with the HIPAA Right of Access, according to a 2019 Citizen Health study. To address this issue, HHS launched a new HIPAA Right of Access enforcement initiative last year.
What Is HIPAA Compliance in IT?
While it’s useful for IT leaders to understand the big picture of HIPAA, the Security Rule is by far the most relevant for HIPAA IT compliance. Healthcare organizations are required to do everything possible to secure PHI and protect it from attack. That’s getting harder to do without skilled, experienced IT engineers who understand HIPAA network requirements.
The vast majority (93 percent) of healthcare organizations have experienced a data breach over the past three years, and 57 percent have had more than five, according to a new Black Book Research survey. Worse yet, 96 percent of healthcare IT professionals believe that data attackers are “outpacing their medical enterprises.”
At the same time that healthcare institutions face increased digital threats, their employees are demanding new digital solutions and smartphone-based clinical communications, and their patients are demanding multichannel communication. These tools give organizations a competitive advantage but can also create a security disadvantage.
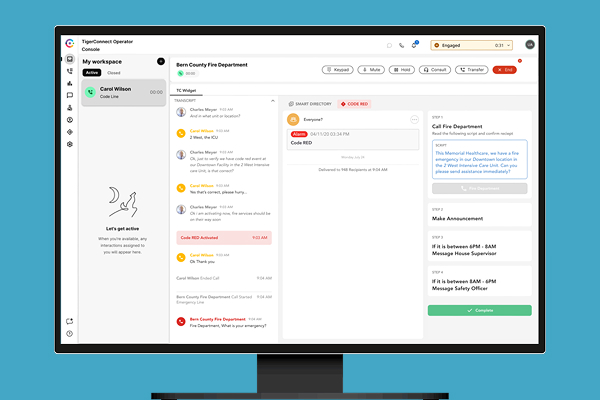
That’s why healthcare leaders are looking to IT for help — not just securing legacy technology and databases against new threats, but also implementing cutting-edge communication solutions that meet strict HIPAA Messaging Compliance guidelines. This is uncharted and risky territory for health organizations, but a HIPAA-savvy IT department can help see them through.
For more on HIPAA in IT, download the eBook “How to Become HIPAA Compliant (Step-by-Step Guide).” Plus, learn more about how TigerConnect meets HIPAA approval.
Featured Resources
Related Articles