How to become hIPAA Compliant (step-by-step guide)
Customer privacy and cybersecurity are critical issues for most industries, but none more than healthcare. Thanks to the Health Insurance Portability and Accountability Act (HIPAA), health data is highly protected. It’s also the most valuable data on the black market, where medical records are worth $250 apiece. The next highest price tag is just $5.40 for payment records.
Hackers aren’t the only HIPAA security threat. Loose lips, unencrypted messages, and unlocked server room doors can also lead to expensive violations. To protect patient health information and the organization’s bottom line, healthcare organizations must know how to become HIPAA compliant.
What is HIPAA compliance? Who needs to comply? And what does it take to build a robust HIPAA compliance program?
Who Needs to Be HIPAA-Compliant?
HIPAA Privacy and Security Rules require compliance from all “Covered Entities” and their “Business Associates.”
Covered Entities are healthcare organizations or professionals that create, maintain, or transmit protected health information (PHI) — including healthcare providers such as doctors, nurses, hospitals, and pharmacies, as well as health plans and healthcare clearinghouses.
Business Associates are service providers or professionals who carry out healthcare functions or activities on behalf of covered entities and need PHI access to do their jobs. Business associate categories include:
- Legal
- Actuarial
- Accounting
- Consulting
- Data Aggregation
- Management/Administrative
- Accreditation
- Financial
What Are the HIPAA Rules?
Congress passed HIPAA legislation in the mid-1990s, with two goals in mind: to improve the portability of health insurance when people changed jobs and to reduce healthcare fraud and waste. Since then, the Department of Health and Human Services (HHS) has added a series of HIPAA rules that require healthcare organizations — and their business associates — to protect patient privacy and secure patient data. The rules include:
HIPAA Privacy Rule
The Privacy Rule sets national standards for the protection of “individually identifiable health information” — which includes information about a patient’s mental or physical health, medical treatments, or payment history. Healthcare organizations and providers are required to protect this information “in any form or media, whether electronic, paper, or oral” when it contains PHI such as name, phone number, birth date, Social Security Number, or any other personal identifier.
Simply put, any medical information that can be tied to a specific patient is protected by HIPAA.
The HIPAA Privacy Rule outlines how healthcare providers can use patient data, what they can disclose without the patient’s permission, and to whom. The rule also guarantees patients the “Right to Access” most of their personal health information and obtain copies of their medical records. Healthcare providers are required to develop and implement written privacy policies for their organizations, to notify patients (in writing) about these policies, and to provide annual HIPAA training for staff.
HIPAA Security Rule
The HIPAA Privacy Rule requires organizations to secure PHI. The Security Rule tells them how to do it. More specifically, the Security Rule sets national standards for the protection of electronically protected health information (ePHI) — including how that data should be handled, maintained, and transmitted.
This rule requires healthcare organizations to have three types of data security safeguards in place — including administrative, physical, and technical safeguards. (More on all three below.)
HIPAA Omnibus Rule
HHS enacted the final Omnibus Rule in 2013 to address policy gaps in earlier HIPAA rules. Most notably, the Omnibus Rule defines the role of business associates, which were not previously subject to HIPAA rules, and outlines the criteria for Business Associate Agreements (BAAs).
The Omnibus Rule also introduced new provisions required by the Health Information Technology for Economic and Clinical Health (HITECH) Act — part of the American Recovery and Reinvestment Act of 2009. The HITECH Act incentivized the use of EHR in the U.S., strengthened HIPAA security and privacy protections, and increased the legal and financial liability for non-compliant organizations.
Breach Notification Rule
The Breach Notification Rule requires covered entities and business associates to notify OCR when ePHI has been breached. HHS defines a breach as “an impermissible use or disclosure under the Privacy Rule that compromises the security or privacy of the protected health information.” The Breach Notification Rule outlines which types of breaches must be reported and how.
The rule also distinguishes between “minor breaches” (those affecting fewer than 500 people) and “meaningful breaches” (those affecting more than 500 individuals). HIPAA requires organizations to report types of breaches to OCR, but the protocol is different, and all meaningful breaches are made public on OCR’s Breach Notification Portal, or “Wall of Shame.”
HIPAA Enforcement Rule
The Enforcement Rule empowers HHS to enforce the Privacy and Security Rules. It gives OCR the authority to investigate HIPAA complaints, conduct compliance reviews, perform education and outreach, and levy fines of up to $1.5 million. Last year, OCR penalized 10 organizations, for a total of $12.27 million. OCR also works with the Department of Justice to refer possible criminal violations of HIPAA.
How to Become HIPAA Compliant in 7 Steps
What does it take for healthcare organizations to achieve HIPAA compliance?
1. Create Privacy and Security Policies for the Organization
Becoming HIPAA compliant requires more than simply following HIPAA Security and Privacy Rules. Covered entities and business associates must also prove that they’ve been proactive about preventing HIPAA violations by creating privacy and security policies. These policies must be documented, communicated to staff, and regularly updated. Staff must be trained on HIPAA policies during orientation and at least once a year, and they must attest (in writing) that they understand all HIPAA policies and procedures.
Healthcare organizations are also required to create and distribute a Notice of Privacy Practices (NPP) form for patients to review and sign. The NPP should outline the covered entity’s privacy policies, including how PHI is handled, and notify patients of their right to access copies of their medical records.
2. Name a HIPAA Privacy Officer and Security Officer
HIPAA legislation is complicated and ever-changing, so every healthcare organization needs its own internal HIPAA experts.
The HIPAA Security Rule requires covered entities to designate a Privacy Compliance Officer to oversee the development of privacy policies, ensure those policies are implemented and update them annually. HHS suggests that larger organizations also form a Privacy Oversight Committee to help guide policy creation and manage oversight. The Privacy Officer and Oversight Committee members must undergo regular training to stay abreast of changes to HIPAA regulation. The HIPAA Privacy Officer is also responsible for maintaining NPPs, managing and updating BAAs, scheduling training sessions and self-audits, and otherwise ensuring that the organization is compliant with the HIPAA Privacy Rule.
Covered entities are also required to have a HIPAA Security Officer to ensure there are policies and procedures in place to prevent, detect, and respond to ePHI data breaches. The Security Officer establishes safeguards required by the Security Rule and conducts risk assessments to gauge their effectiveness.
3. Implement Security Safeguards
The Security Rule requires three types of safeguards that covered entities and business associates must have in place to secure ePHI — including:
- Administrative Safeguards: Organizations must document security management processes, designate security personnel, adopt an information access management system, provide workforce security training, and periodically assess all security protocols
- Physical Safeguards: Organizations must be able to control who has access to physical facilities where ePHI is stored. They must also secure all workstations and devices that store or transmit ePHI.
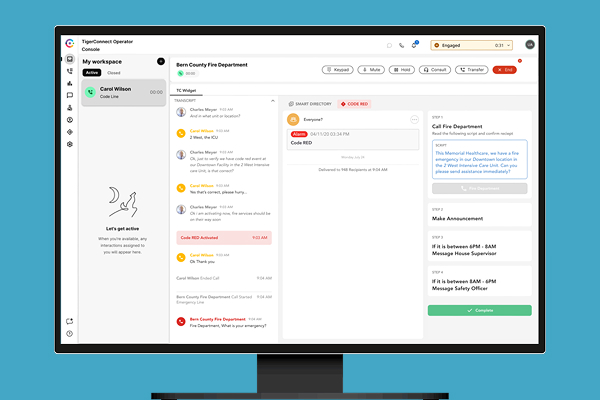
- Technical Safeguards: Organizations must have access controls to secure ePHI in the EHR and other databases to ensure employees only see data they’re authorized to see. Data must be encrypted when it is at rest and during transit, which creates the need for secure email, HIPAA Compliant Texting, and HIPAA Compliant Messaging solutions. Organizations must also have audit controls for all hardware and software that manage or transmit ePHI to ensure they meet HIPAA network requirements. And there must be integrity controls to ensure ePHI is not improperly edited or deleted.
For covered entities needing HIPAA compliance help, HHS has developed guidance materials, checklists, and risk assessment tools that clearly outline how to become HIPAA compliant.
4. Regularly Conduct Risk Assessments and Self-Audits
Becoming HIPAA compliant is not a one-and-done process. HHS requires covered entities and business associates to conduct regular (at least annual) audits of all administrative, technical, and physical safeguards to identify compliance gaps. Organizations must then create written remediation plans that clearly explain how they plan to reverse HIPAA violations and when this will happen.
5. Maintain Business Associate Agreements
Before sharing PHI with business associates, covered entities must obtain “satisfactory assurances” that the business associate is HIPAA-compliant and can effectively safeguard the data, and the parties must enter a BAA. All BAAs must be reviewed annually and updated to reflect any changes in the nature of the business associate relationship.
6. Establish a Breach Notification Protocol
A HIPAA violation doesn’t always get organizations into trouble, especially if they can prove the breach was unintentional and that they did everything in their power to prevent such breaches. But failing to report breaches makes the situation worse.
The HIPAA Breach Notification Rule requires covered entities and business associates to report all breaches to OCR and to notify patients whose personal data might have been compromised. HIPAA-beholden organizations are required to have a documented breach notification process that outlines how the organization will comply with this rule.
7. Document Everything
Organizations must document all HIPAA compliance efforts — including privacy and security policies, risk assessments and self-audits, remediation plans, and staff training sessions. OCR will review all this documentation during HIPAA audits and complaint investigations.
HIPAA compliance is critical for healthcare organizations, not only to protect patient privacy but also to protect the bottom line. To keep data safe, healthcare providers need to know how to become HIPAA compliant, and they need technology partners who take it just as seriously as they do.
To learn more, read TigerConnect’s HIPAA Compliance Statement.
Featured Resources
Related Articles