MENUMENU
- Who We Serve
- Solutions
-
Coordinate care across teams and facilities with a full suite of collaboration products to accelerate care delivery.
Integrate with EHR, nurse call, and physiological monitors for prioritized, actionable alerts and notifications.
Standardize communication and streamline workflows on a single, integrated cloud-native platform.
Reach patients and families by text, voice, or video in a way that’s easy for patients. Manage virtual visits and reminders.
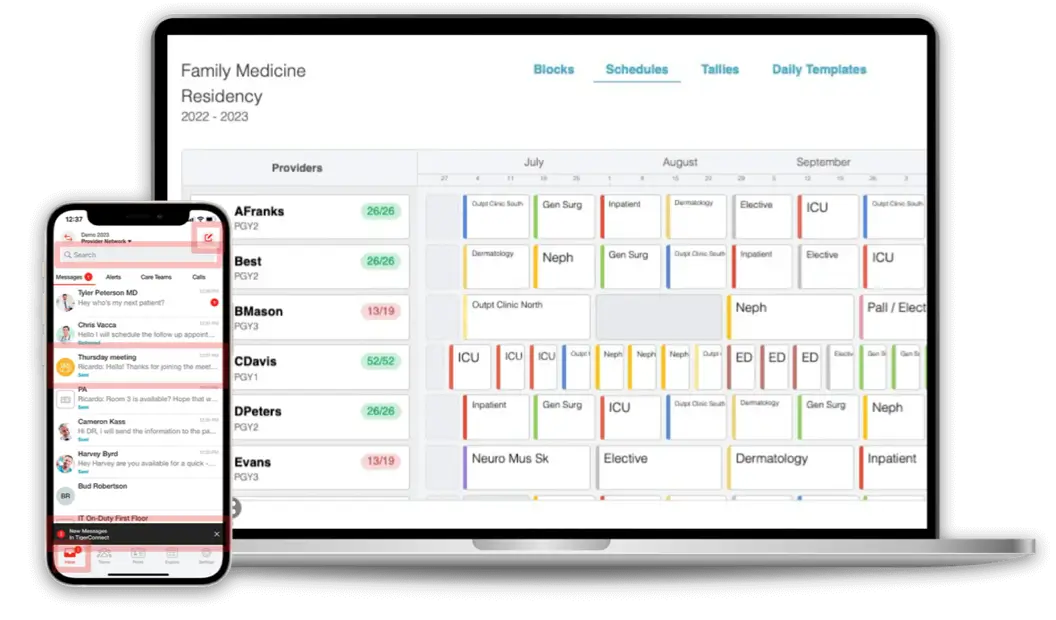
Build and share on-call schedules with ease using templates. View and make shift swaps via mobile or desktop.
-
- Resources
- Why TigerConnect?
- Get a Demo